Mine is a 2020 with 32gb storage and 3gb ram but same ballpark. I just replaced my PC earlier this year but the Chromebook is next. I’m looking at renewed HP elitebooks or renewed ThinkPads, but I’m not sure either come in a size OP would want.
- 3 Posts
- 31 Comments
Came to second this. I have an old hp Chromebook that is indestructible, has insane battery life, and still has a few years of updates left. The built in Linux terminal is fine and just about anything you can get through apt-get, dpkg, or otherwise works fine as well (if there is an arm version), it’ll even add menu entries for GUI apps.
I do light reading or dev work on it, and use the built in terminal to keep track of and ssh into my remote boxes. I take it on the road to take notes or hop on a wifi.
When I first got it the interface was kinda crap for a laptop, but through the updates (dark mode, new menu, etc) it’s actually just fine now.
It’s slow, low ram and only usable for a few tabs at a time, but for what I use it for it does fine, and it was cheap enough I won’t cry if it dies.

 5·3 months ago
5·3 months agoI dual booted a few times back in the days of winxp and win7. Never had a good experience somehow windows or a grub update always messed up things. Haven’t ran windows in years but when I have to it goes on a separate drive now.

 13·3 months ago
13·3 months agoYou can import CSV files directly into an SQLite database. Then you are free to do whatever sql searches or manipulations you want. Python and golang both have great SQLite libraries from personal experience, but I’d be surprised if there is any language that doesn’t have a decent one.
If you are running Linux most distros have an SQLite gui browser in the repos that is pretty powerful.
Just came here to say you could always look for alternative projects that have this built in as well. I’m not sure what logs you as looking at, but it might be best to contribute or request this feature directly for the software.
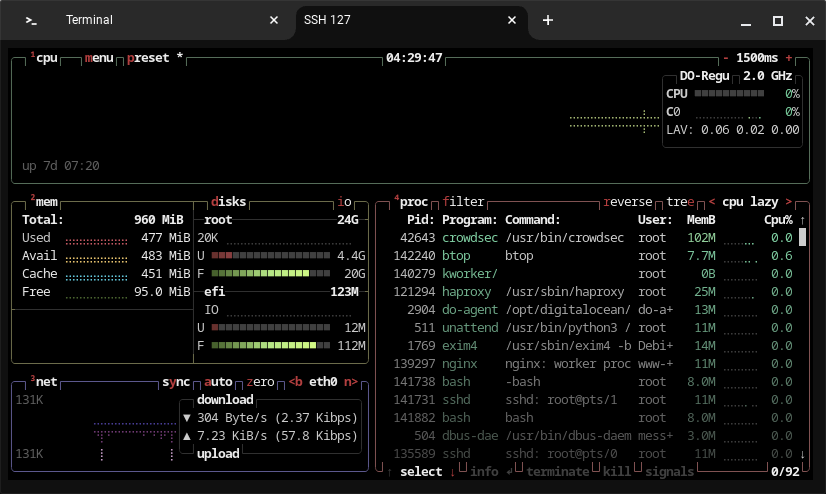
For example I use crowdsec and they have a button on the logs pages that will anonymize the entire page and is great for taking screenshots.
I agree with another poster that getting something to work with a number of different logs would be a huge undertaking and unrealistic for most solo devs. I do think asking whatever project could be a start. I’d love if journalctl and syslogd etc had a flag to anonymize the log output.
Personally often times I just open the screenshot in gimp and pixelate out the areas I want hidden, but that’s not an automated solution.
I second this. I run fedora on my desktop and debian on the server. Docker works great on debian as well.

 1·3 months ago
1·3 months agoThanks that’s good to learn!
I’d suggest one of the fedora atomic installs, maybe even get a couple renewed Thinkpads all set up, one with kde and one with gnome and let them play with them for a few days. I was the only engineer in my company that ran Linux and the bosses only concession was that I carry a windows PC too when he was onsite with me so he’d understand what I was doing, but he provided a nice one for me so I never complained.
No offense taken we all have different knowledge and background. I have a general understanding of podman, but now I’m going to go play with it a bit at some point and get more familiar with it.
Docker is Apache 2.0 licensed. It is open source. Or at least all of the important parts. I’m not sure about docker desktop. It’s partly that I just have a lot of experience with docker, and partly just that it’s what is supported in most projects’ documentation. The fact that a lot of the Linux foundation training uses docker is another reason I’ve got more experience with it.
As far as what you are talking about people have been trying for years. The Pirate Bay wanted to develop a new method of being entirely decentralized. Odysee is working on something like blockchain/torrents combined that is very interesting. We have I2P and TOR which have some of the features you mention. I’d love to see it happen where the big companies didn’t control things.
There is progress though. https://letsencrypt.org/ is non-profit, and there are a variety of open source projects using this to automate TLS certificate signing.
Check out https://www.sigstore.dev/how-it-works and pay special attention to Fulcio and Rekor. It’s not for web certs, but it’s still a very interesting take on a certificate authority.
There’s no technical reason what you are saying couldn’t work. It just comes down to how do you trust it, and if you can’t at all, it doesn’t do much good anyway. That’s the problem to be solved. You could compromise somewhere in the middle but then you have to work out what is acceptable. I suppose the level of trust could be configurable, with different nodes earning a different level of trust, and you could configure your accepted levels for DNS or CA. It’s an interesting idea.
Thanks :) Exactly. I do a lot of development and testing in an alpine linux container, simply because it has much newer versions of libraries and musl c. If I can get it to compile there, and on debian, I’m in good shape as far as compatibility goes. I used to really enjoy Arch and the rolling updates when I was younger, but I’ve gotten to where I don’t want to mess with things constantly changing.
I use python venv for nearly everything I do python, and the way go is setup does make it extremely easy since it uses a per user environment anyway.

 1·3 months ago
1·3 months agoI knew that worked for a lot of stuff. That used to be what I’d try first but I honestly just use a venv for pretty much anything that uses pip nowadays. Still helpful to know there is a package though thanks! I intend to test it out.
Hugo is a static website generator used frequently for blogs. hugo bear blog is just one of the themes for it I happened to like so I used it. It does build reactive sites so that they look good on a phone or a pc.

 1·3 months ago
1·3 months ago😱 I had no idea. I just went and read through that wow. I hope they don’t sell to someone scummy.

 2·3 months ago
2·3 months agoI could have swore I tried it. facepalm I’ll check that out then I might edit that part.

 2·3 months ago
2·3 months agoNice. I might have to clone that setup for fun. What do you use for CI? I’ve got jenkins running but I’ve been wanting to play with gitlab CI/CD too.
I do a lot of my dev work in docker containers, simply so I’m in a clean environment. Doesn’t hurt in ease of backup either. No particular reason not to use docker, I also wanted to keep it kind of brief and simple. The guide I originally read that inspired me had a lot of things that were very outdated, and as I worked through getting it working on debian 12 I generally stuck with the source providers instructions when things weren’t already packaged for dpkg, or alternatives were more complex.
I am currently mulling around doing extensions on this guide and adding links at the bottom, or just extending this one a bit. Also just thinking about writing a guide for other stuff too. I’ve been helping people on discord and irc a bit recently and some of what I know might be useful to someone.
I don’t know everything by any means far from it, but I’ve been around since my first beOS and slackware installs a long time ago and I’ve picked up a lot. I worked developing and deploying pfsense images for a company years ago and have just had a lot of random experience in linux and bsds over the years.

 3·3 months ago
3·3 months agoAwesome it is good to see the bearblog getting some love. Just to keep it short mostly. I was debating adding another article continuing this one using nginx for that part. I could add a section to this one though. Or would you use something other than nginx, I’m open to suggestions. I checked yours out, it’s a bit snappier than mine :) . What are you running?

 1·3 months ago
1·3 months agoExcellent thank you! I’ll check this out.

 1·3 months ago
1·3 months agoAwesome I’ll look into it for sure!

 1·3 months ago
1·3 months agoOh gotcha. It was late when I replied :p. You absolutely get security with a layer of separation from hosting remotely. I monitor my home network and have a similar setup but I don’t host anything from here. I never get attacked or probed at all compared to my remote server. Just having those open ports makes you a target. Once a few scanners pick up on you hosting content you will absolutely start getting attacked. Another benefit is you don’t have to have any passwords on your remote host, just an ssh key. They can bruteforce all they want, good luck without a zero day. You also keep your personal IP address out of peoples scope by not hosting from the local network.
I used to run much heavier protection on my home network, but after keeping an eye on all the logs and alerts for a while I realized I was just wasting ram and storage space mostly. Sane firewall settings is enough for a typical home, and something like crowdsec is probably overkill.
Now if you are hosting stuff it’s a different story. I would actually harden my local network MORE than I did the remote one due to much more of my personal stuff being on my local network. My remote host being compromised would be a mild hassle at most, It does self backups once a week, and I have my entire site in a private git repo I sync to. It would take a few minutes to throw up another server, if my home stuff got compromised a lot more damage could be done.
https://gitlab.gnome.org/chergert/ptyxis
Ptyxis is my current go-to. It can detect available pods or toolboxes (maybe docker too haven’t tested it) and you can open terminals directly into them. It also highlights ssh terms and root shells differently.
There are a huge number of built-in color schemes as well and I’ve had no trouble finding any configuration option I’ve found myself wanting to look for.
It’s also available on flathub so it’s easily installed in most distros.